History says TYPO3 is one of the most secure OpenSource CMS. But, security is a never-ending task, In this article, I want to introduce Helmut’s popular “TYPO3 Secure Web” package to more secure your TYPO3 site.
We as a whole see that it is so essential to maintain the TYPO3 Security of your site. Google blacklists around 10,000+ websites every day for malware and around 50,000 for phishing continuously.
Fortunately, TYPO3 has better built-in firewall security because the core architecture of TYPO3 is robust. But, TYPO3 security never-ends. The TYPO3 community is always serious about security and performance, and always develops something which improves security.
“If you spend more time on coffee than on IT security, you will be hacked. What’s more, you deserve to be hacked.
- Richard Clarke”
TYPO3 - Most Secure OpenSource CMS
According to the report of Sucuri.net TYPO3 is the world's least hacked OpenSource CMS.
Source
A hacked TYPO3 site can make genuine harm to your business income and notoriety. Hackers can take client data, passwords, introduce noxious programs, sell information, and can even multiply malware to their clients.
Most noticeably awful, you may wind up paying ransomware to hackers just to recover access to your very own website.
public | that only contains assets like css/js/images etc., for the web public users. |
private | that contains typo3 core sysext, typo3conf ext, etc., |
var | that contains cache, log, session, etc., |
vendor | that contains CMS as well as extension’s vendors. |
Applause to Helmut Hummel
Sounds fascinating right? We serve gratitude to Helmut for his 10+ long years of contribution and commitment to the TYPO3 Community - particularly on TYPO3 security.
I would love to present his extraordinary TYPO3 secure web bundle https://github.com/helhum/typo3-secure-web
It's an ideal opportunity to acknowledge and state our "much appreciation for Helmut" by staying in contact and being associated with him at:
- Twitter: https://twitter.com/helhum
- Github: https://github.com/helhum
- Blog: https://insight.helhum.io/
IMHO: Someday, we wish typo3-secure-web package gets included within the TYPO3 core!
Did you know?
TYPO3.org project has been secured with this package typo3-secure-web :)
Step-by-step Guide to TYPO3 Secure Web
Pre-requisite and Dependencies
Package | Description |
typo3/cms-core | ^8.7.10 || ^9.5.2 || ^10.4 |
typo3/cms-composer-installers | ^1.4 || ^2.0 || ^3.0 |
helhum/typo3-composer-setup | ^0.5.4 |
Care to the Conflict
Package | Description |
helhum/typo3-composer-setup | <0.5.4 |
typo3/cms | <8.7.10 |
typo3/cms-core | <8.7.10 |
Let’s get ready to implement a TYPO3 secure web package to your composer based TYPO3 installation, Our technical team develops TYPO3 projects with best practices of Docker, DDEV, Composer as below.
Step 1: Create a project folder
mkdir my-typo3-site
cd my-typo3-site
Step 2: Configure PHP version
ddev config --project-type php --php-version 7.2
Step 3: Download latest version through Composer
ddev composer create typo3/cms-base-distribution ^10 --no-interaction
ddev config --project-type typo3
ddev start
Step 4: Run TYPO3 Installation Wizard
touch public/FIRST_INSTALL
Step 5: At composer.json, Setup private and public folders
"extra": {
"typo3/cms": {
"root-dir": "private",
"web-dir": "public"
}
}
Step 6: Secure your TYPO3 with folders structure private and public
ddev composer require helhum/typo3-secure-web
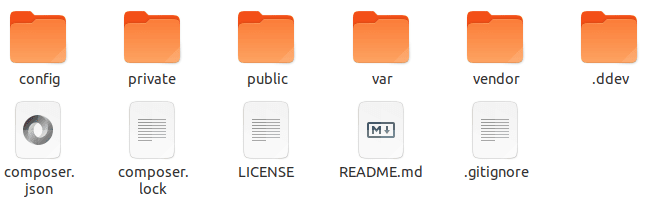
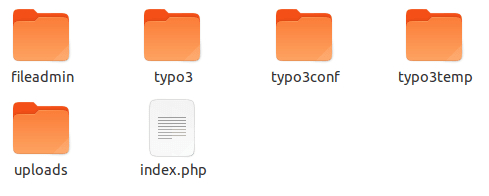
When you have effectively installed TYPO3-secure-web bundle, it will organize entire files and folders architecture at your server as follows:
- This bundle will at that point set up the web server document root inside the public folder and TYPO3 inside the private folder.
- The private folder will look familiar and will contain typo3, typo3conf, fileadmin, typo3temp, uploaded folders
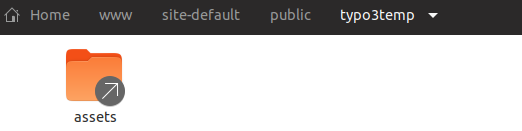
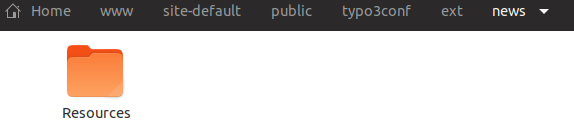
- The public folder will just have the entry scripts and connections to fileadmin, typo3temp/assets and, Resources/Public of all installed (framework) extensions.
Access to Private
Access to Public
Conclusion
- In spite of the fact that the TYPO3 is made robust and secure, Let's keep it safer through the extraordinary typo3-secure-web composer package.
- Remember to say "thanks and Donate to Helmut" for his extraordinary endeavors to the TYPO3 people community.
Are you encountering any issues during setup? Please feel free to connect with us for support. Do you know any other tips and tricks to secure TYPO3? We would love to receive your feedback in the comment box below.
Inspiring People To Secure!
Post a Comment
-
Great Article Sanjay. Thanks for sharing tips and Helhum's security architecture. One of the easiest ways to test security things like this is to clone to a staging or dev environment, run your updates, verify everything is good. And then run it on production.













Sanjay Chauhan
CTO at T3Planet & NITSANSanjay Chauhan, Co-Founder of NITSAN (Award winning TYPO3 agency) and Pioneer of T3Planet (first-ever TYPO3 Store).
A true TYPO3 fanatic since 2010. I bring strong TYPO3 experience in building customer-business…
More From Author